This document describes the procedure for creating a Let's Encrypt certificate on macOS. To verify the functionality of the created certificate, we will install it on Windows Server 2025 and confirm its operation.
This time, we will assume you are creating certificates on a macOS environment. Additionally, a separate web server environment accessible over the internet is required.
Setting up your macOS environment
To create a Let's Encrypt certificate, we'll use the command-line tool called Certbot this time.
Let's proceed with the installation.
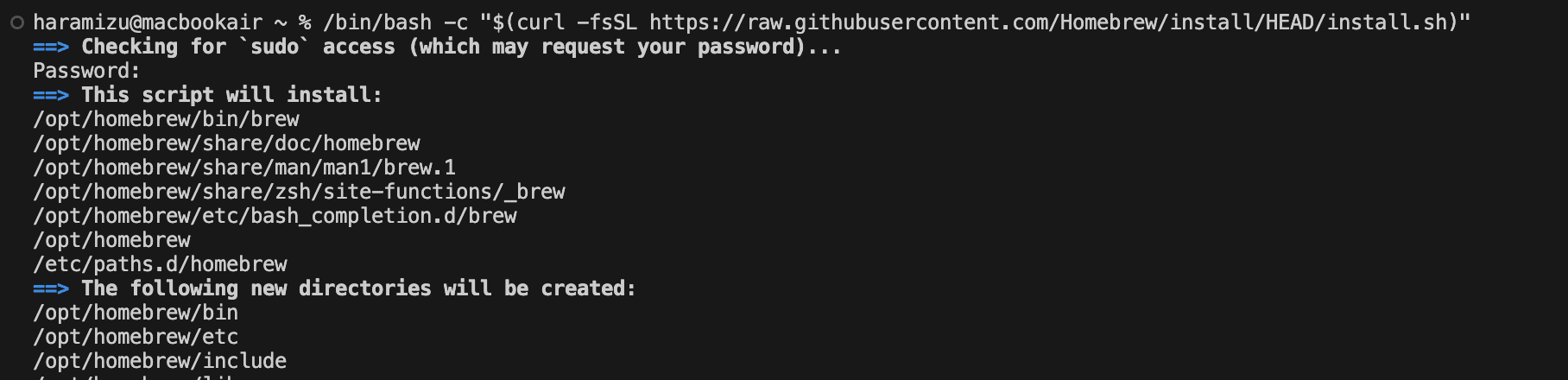
Installing Homebrew
To create certificates, you need to install Certbot as a command-line tool. If installing on macOS, install Homebrew to install certbot. If it's already installed, proceed to the next step.
After installation is complete, verify the version. This time, the version is as follows.
Installing Certbot
Next, install Certbot.
The command is now ready.
Certificate Creation
This time, we will create a certificate for the site test.haramizu.com (note that this site does not exist at the time of this blog's publication). First, prepare a site accessible via HTTP. Personally, I'm familiar with it, so I launched it using IIS on a Windows Server machine.
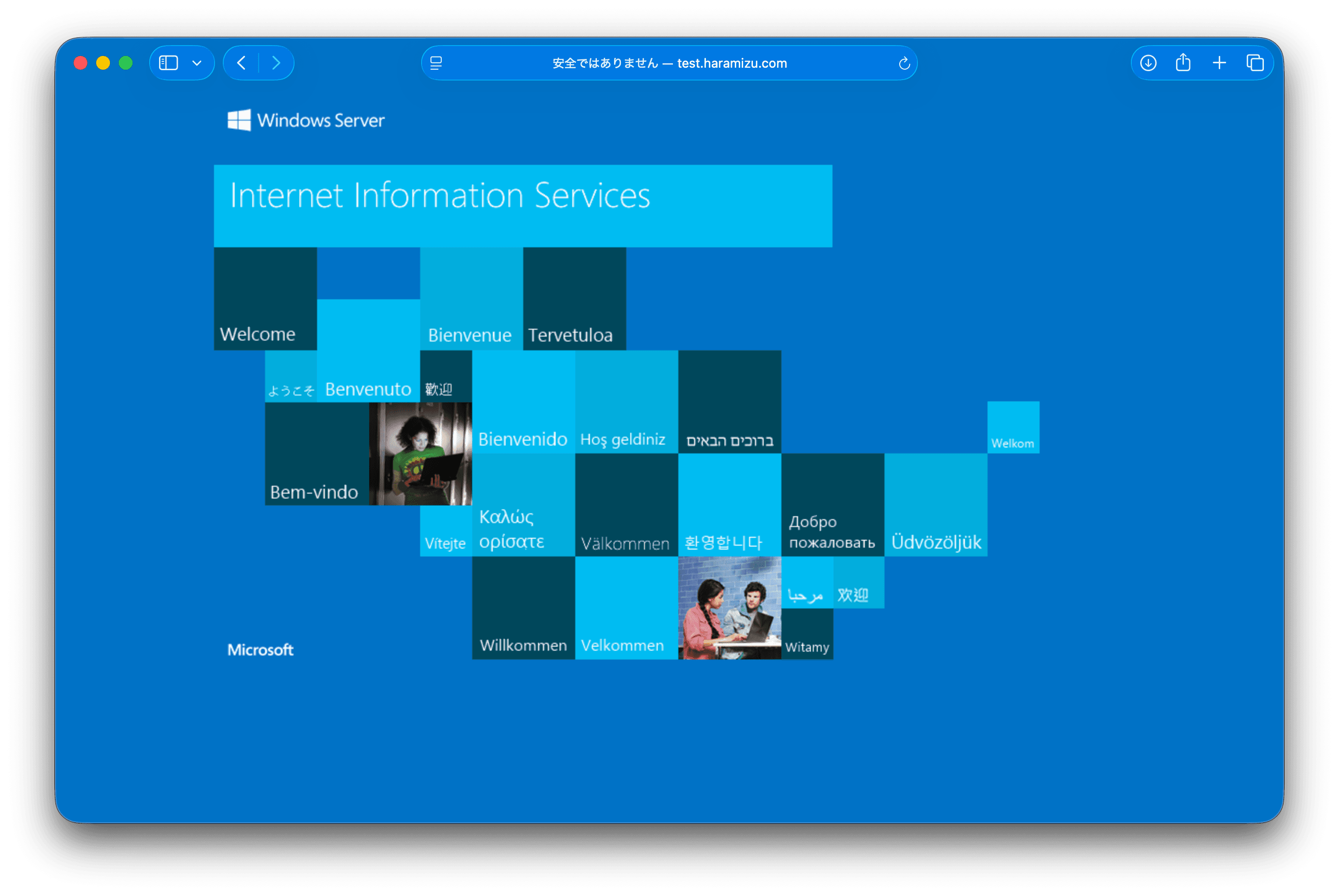
After confirming you can access this server, execute the following command:
When you run the command, information about the string and URL will be displayed (partially masked).
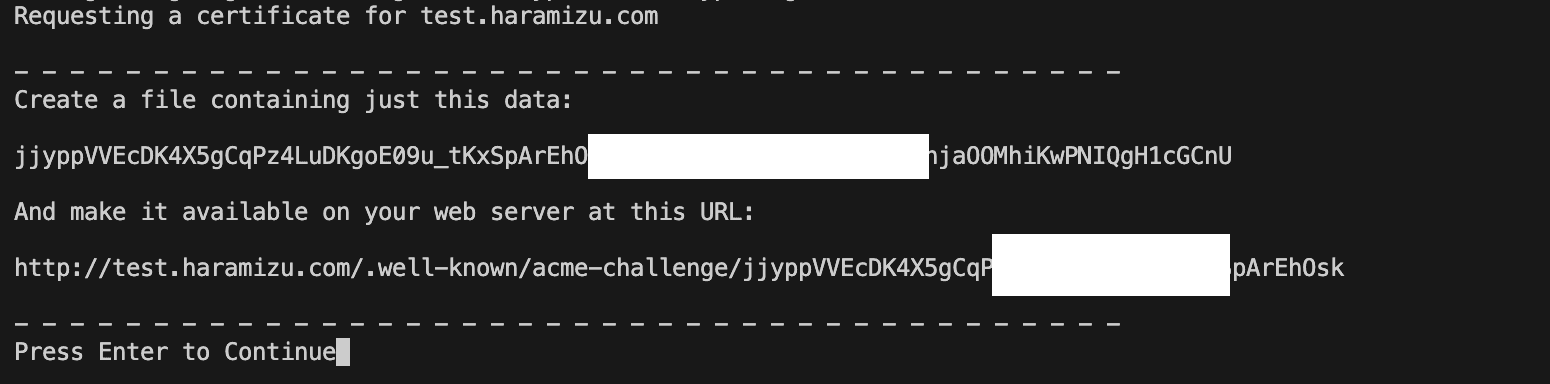
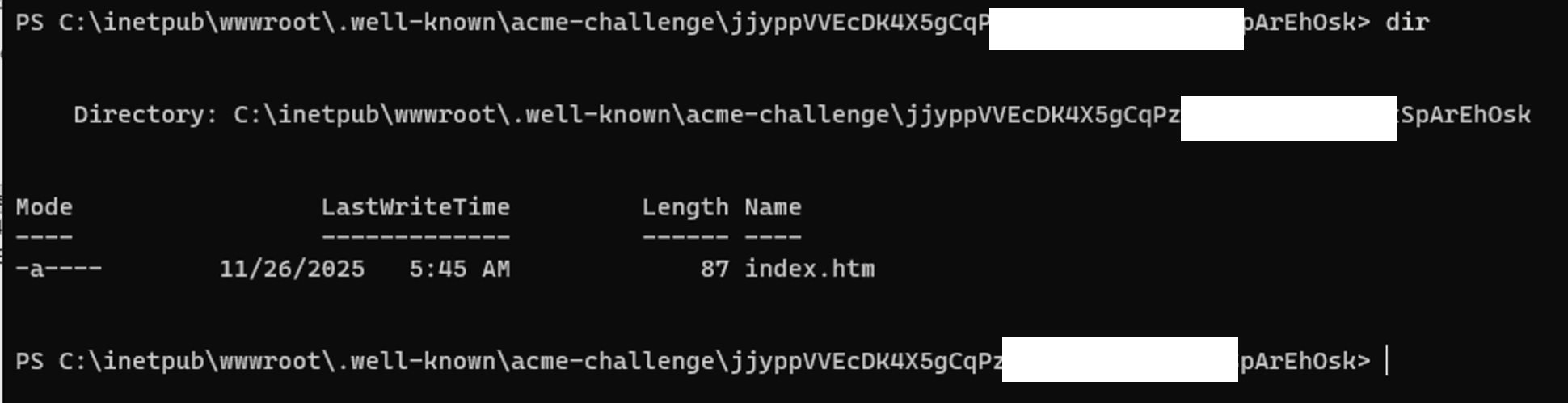
Following these instructions, create a file that displays the specified string when accessed via the URL. Create several directories under inetpub¥wwwroot, and finally create an index.htm file.
The contents of the index.htm file can consist solely of the specified characters. Once the file is created, verify that the string appears at the specified URL.
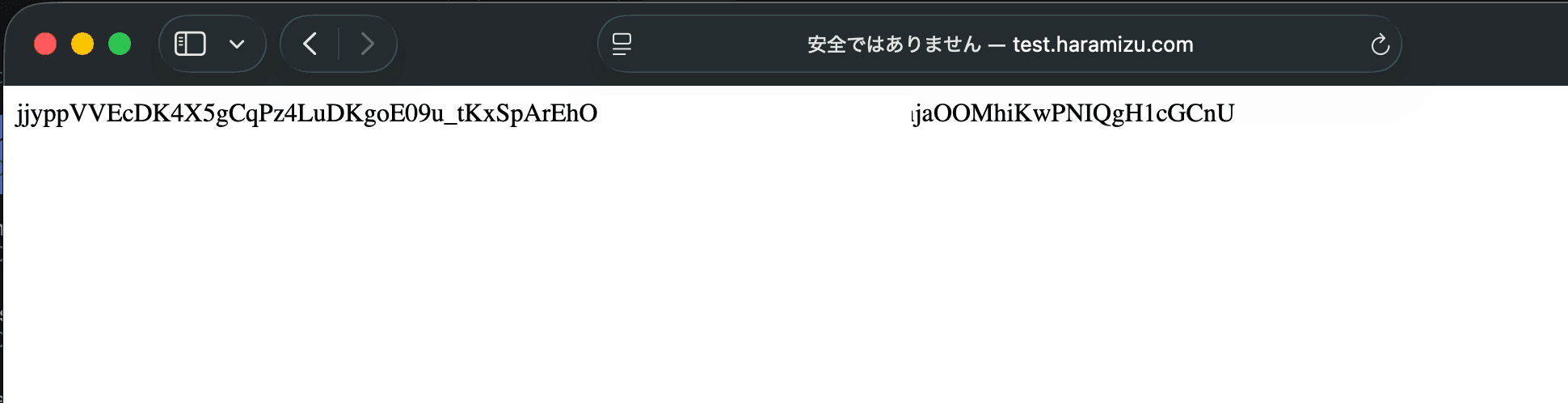
With preparations this far along, I had paused the command, so I clicked Enter. As a result, the file was created as shown below.
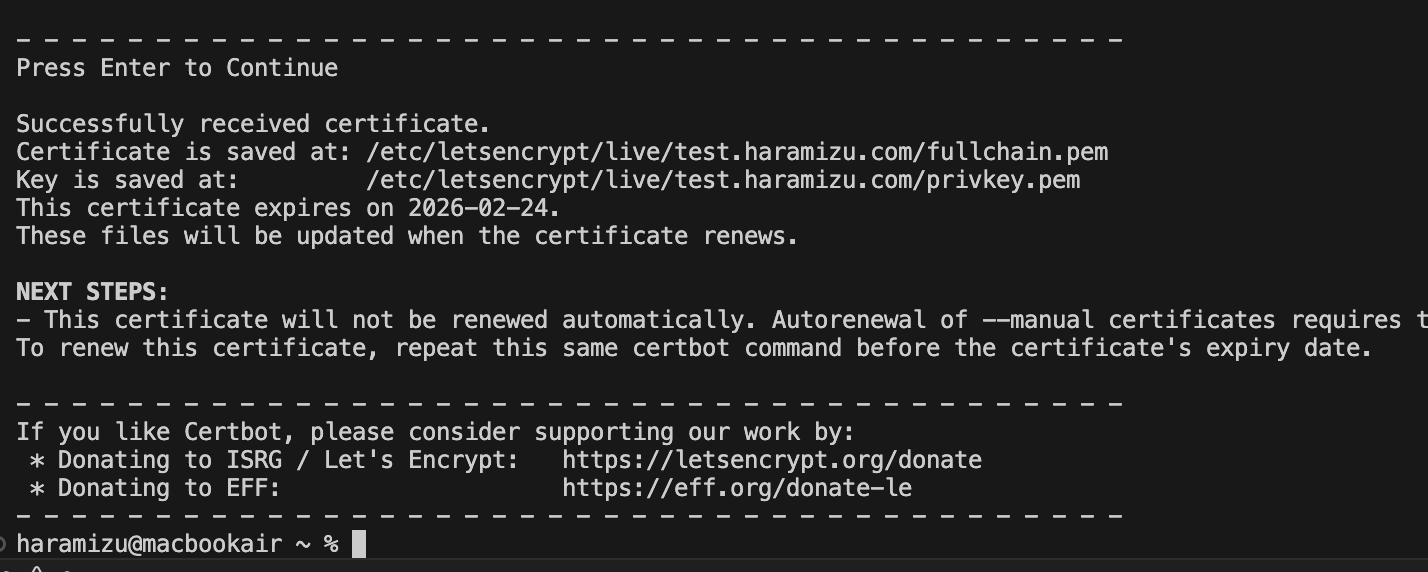
Certification install
Installing OpenSSL
To verify whether the certificate functions correctly, we will use IIS for this test. First, since IIS cannot directly use the PEM format created this time, it must be converted into a PFX file. OpenSSL provides the command to perform this conversion.
The Windows version of OpenSSL can be downloaded from the following site.
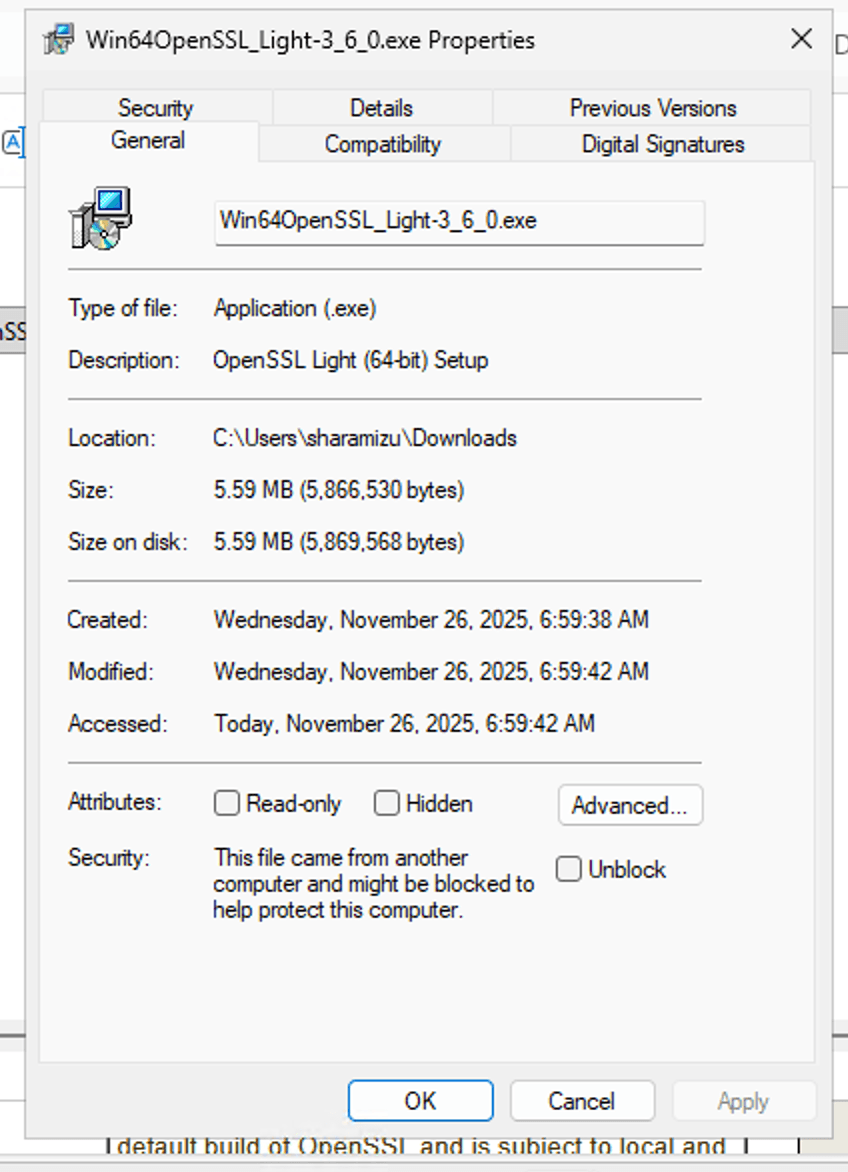
Please download the exe file from the above site. After downloading, open the file's properties, check the "Unblock" box, and then run the installation.
If the runtime is missing, you will need to download and install it. If the runtime is present, you will see a screen like the following.
This will install the command.
Certificate Creation
Next, use the OpenSSL command to create a PFX file. Copy the PEM file already created by Certbot to the `¥temp¥cert` folder.
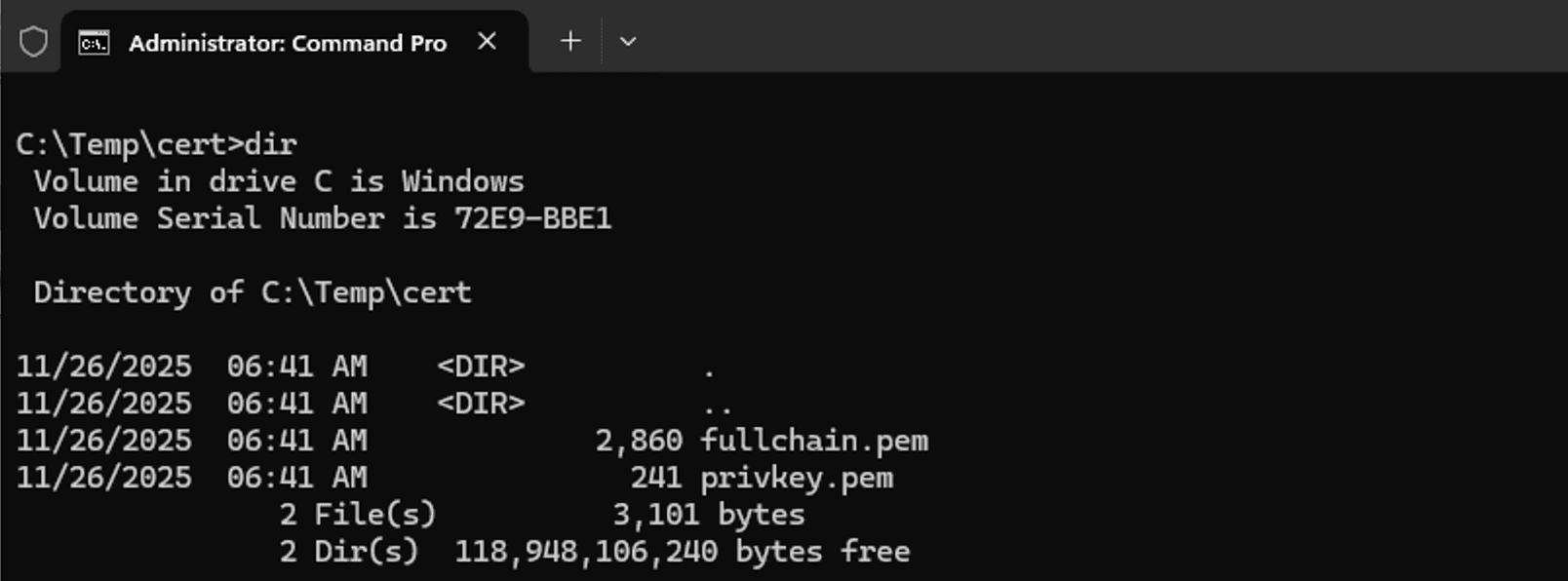
Once the copying is complete, launch the Command Prompt (not PowerShell). Verify that the Command Prompt appears as follows:
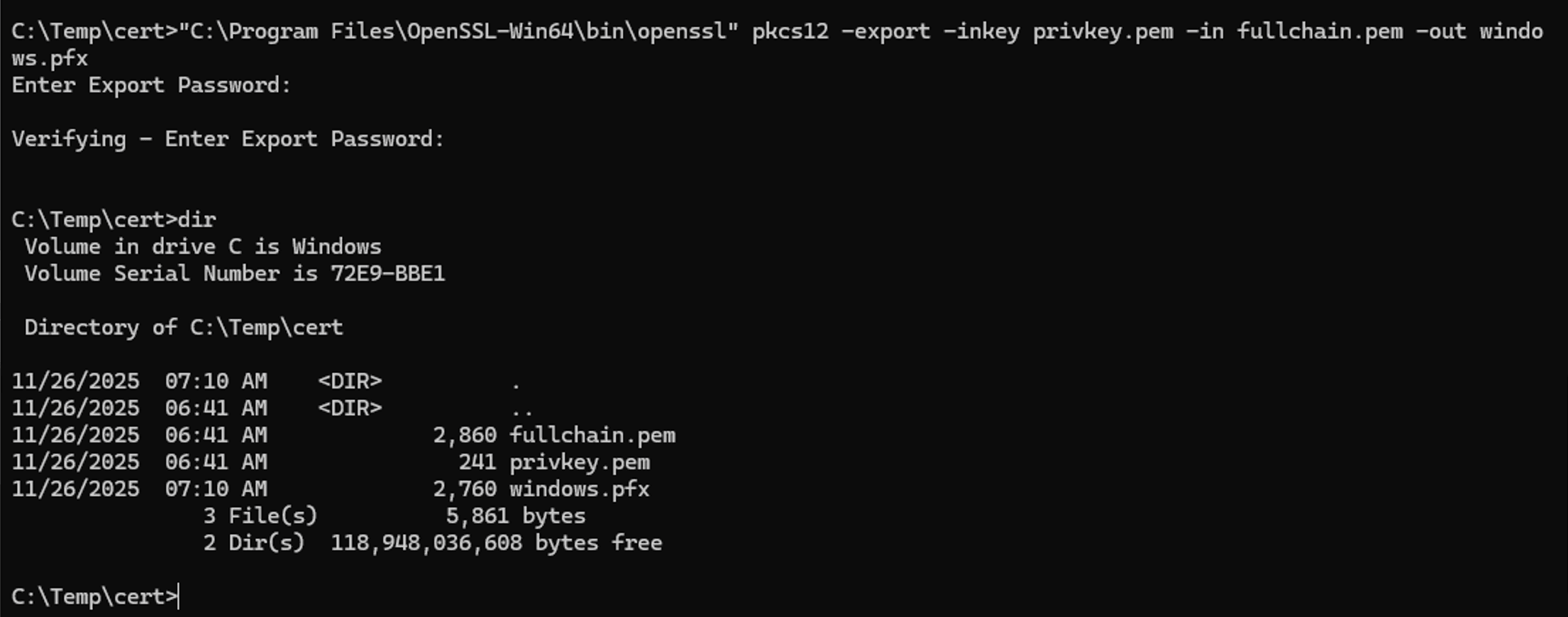
Please execute the command as follows in this path. If the path is set for the openssl command, executing it directly from the command line is fine.
When you run the command, a password confirmation prompt appears, and ultimately a windows.pfx file is created.
Installing the Certificate
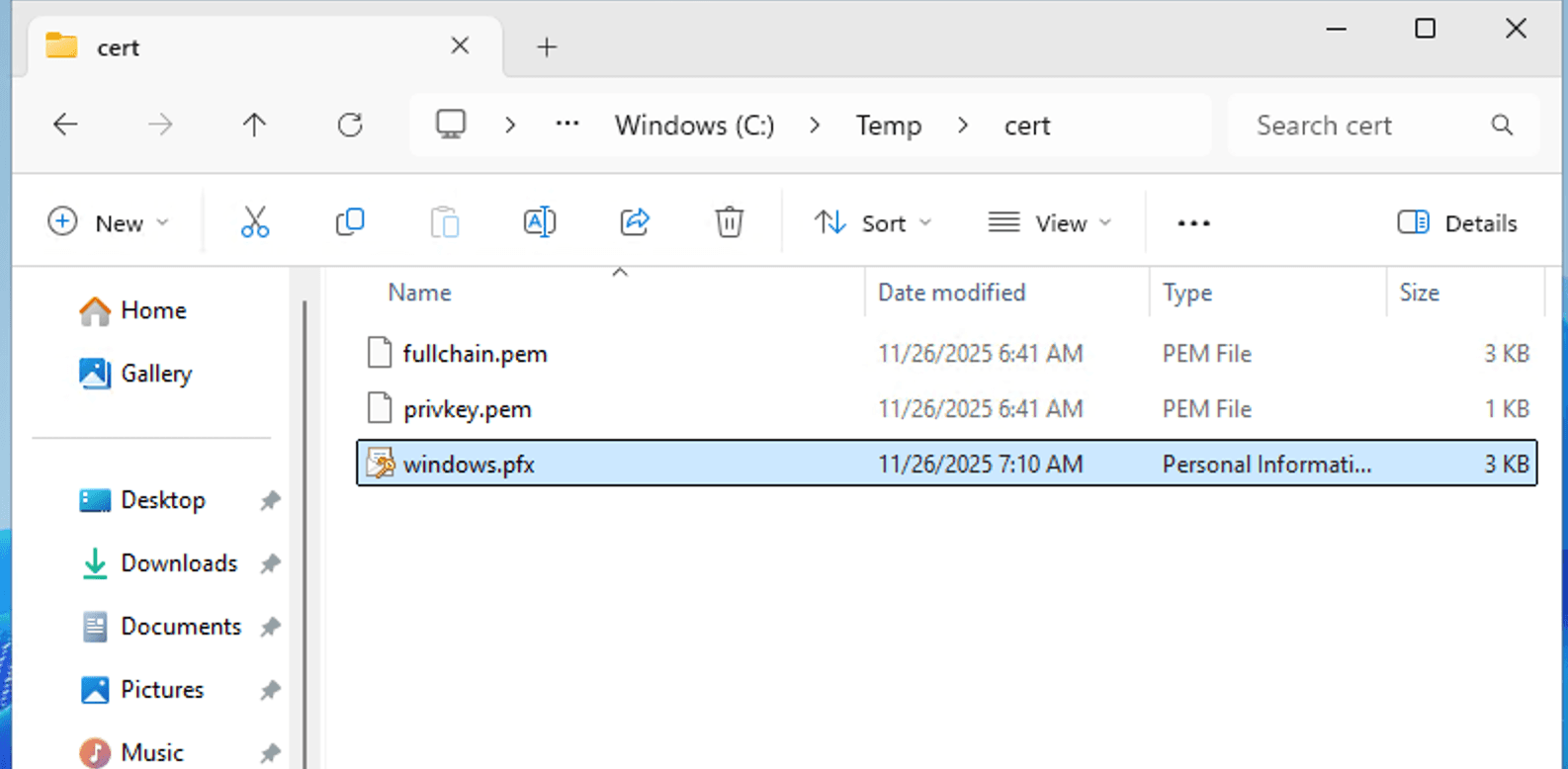
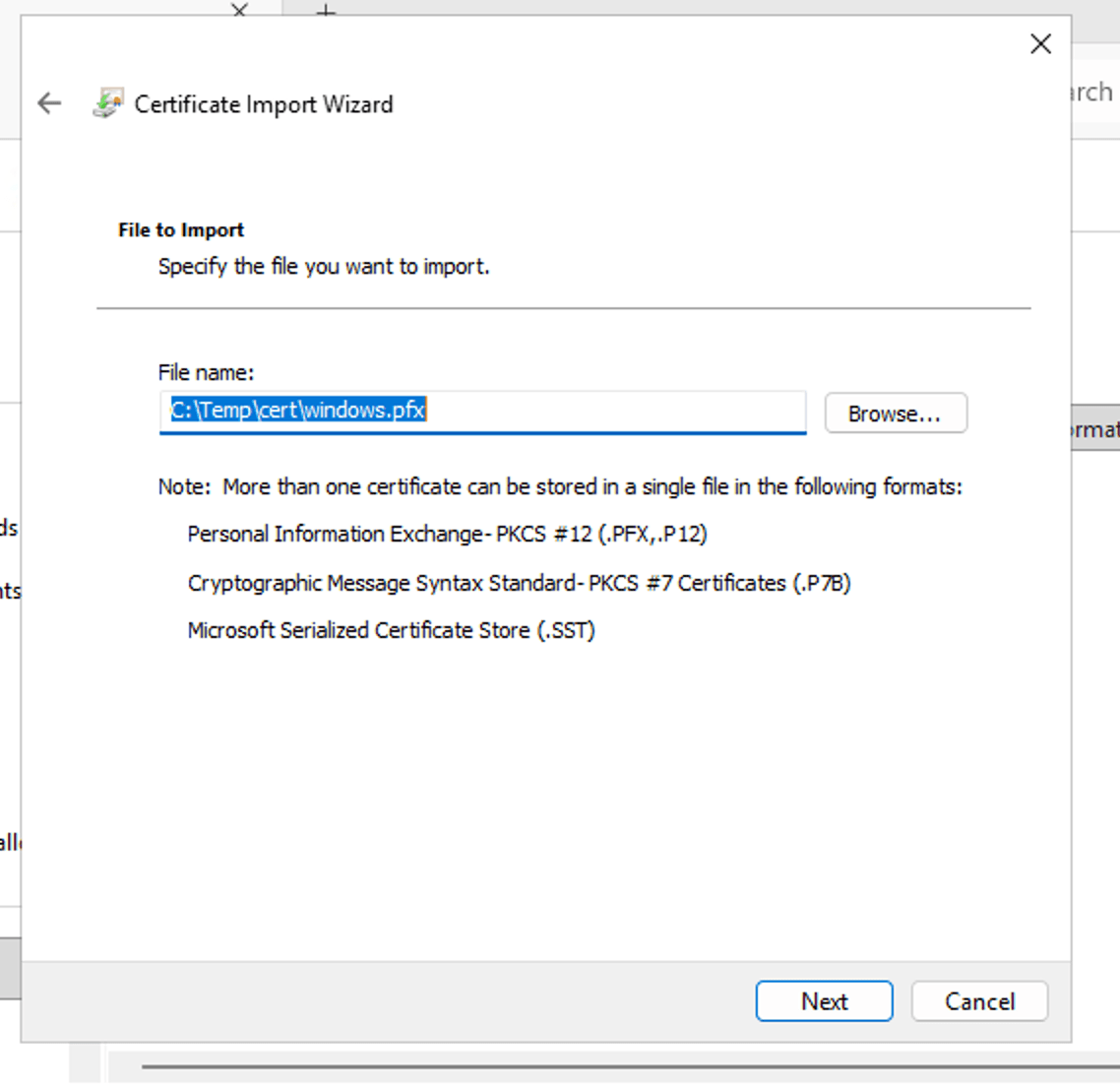
Open the created PFX file in File Explorer and double-click it.
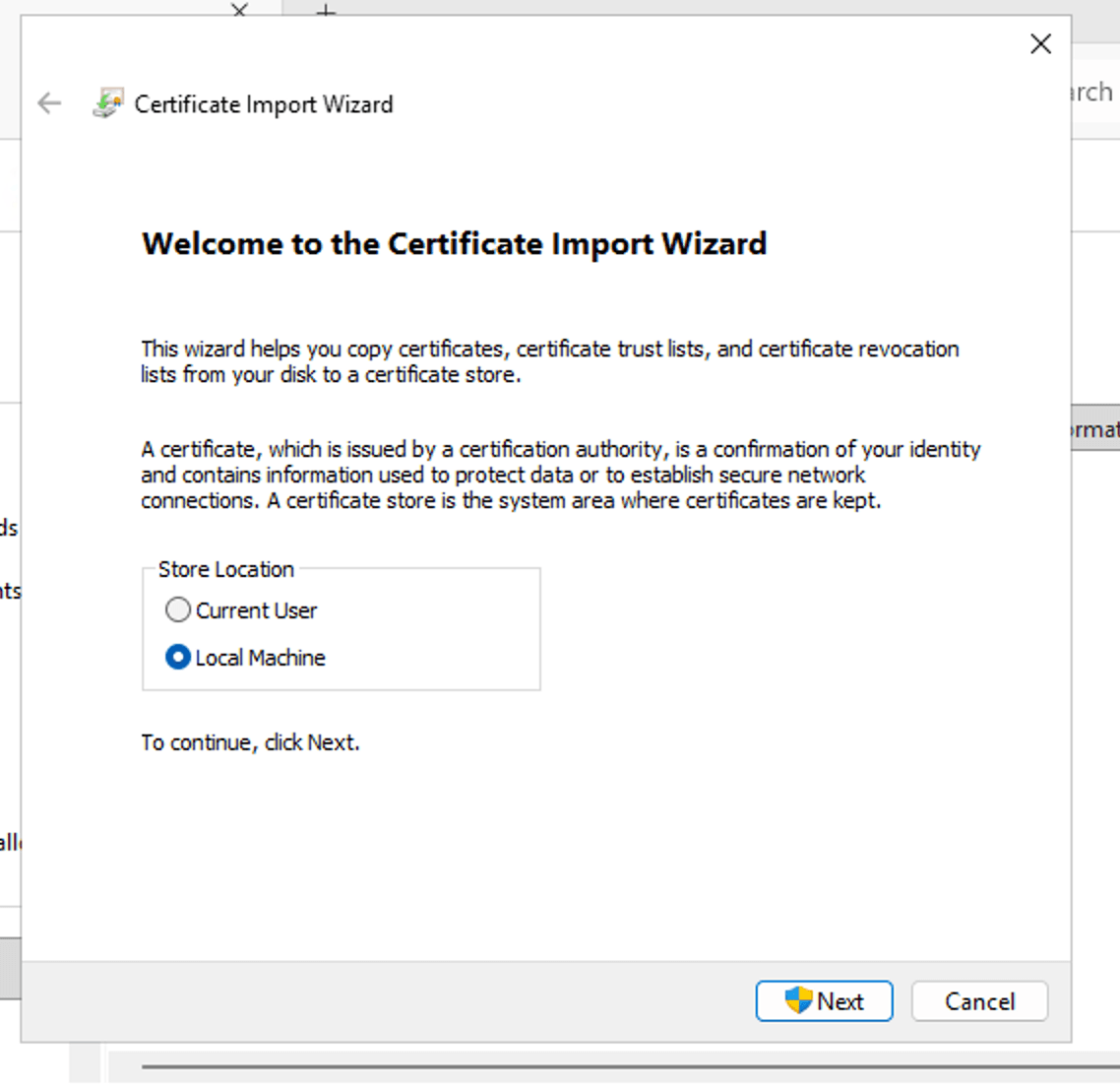
The certificate installation wizard will start. Select Local Machine as the installation destination.
Click Next to proceed to the file selection screen for importing. Click Next again on the following screen.
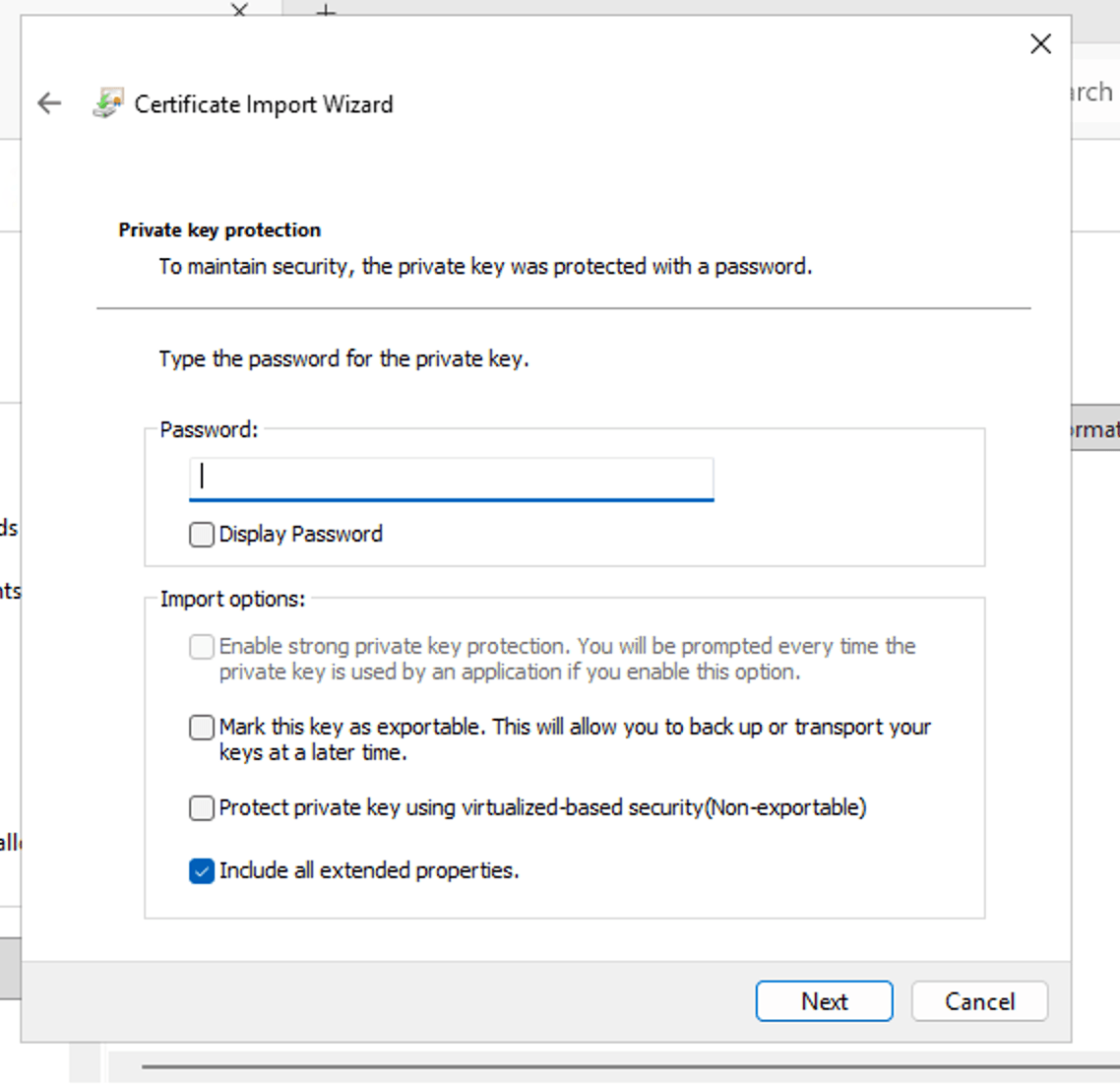
This screen prompts you to enter the password you set when creating the certificate. After entering the password, click Next.
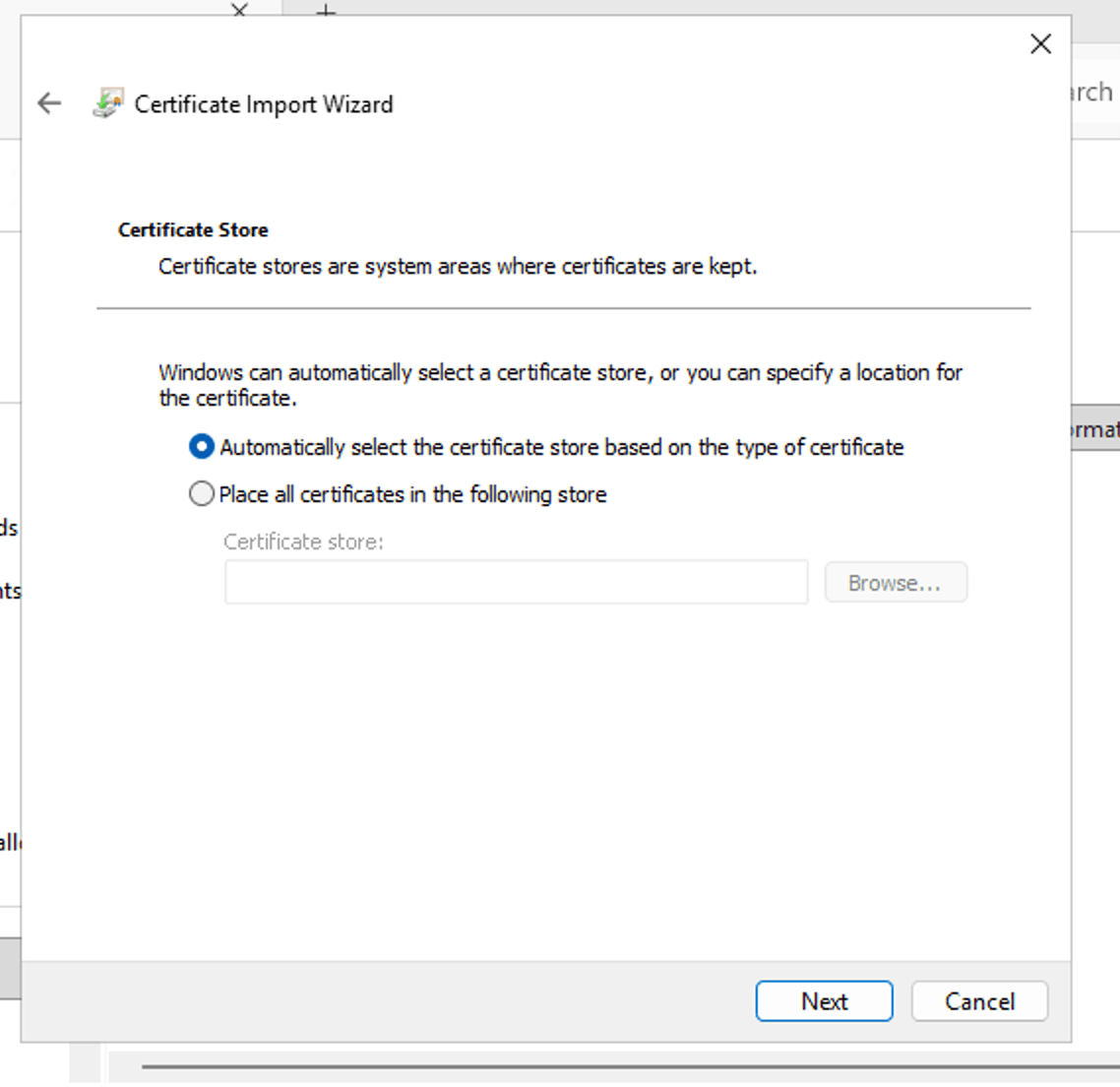
For the installation location, select the Automatically option and click Next. The installation will complete on the next screen.
Apply the certificate to the site
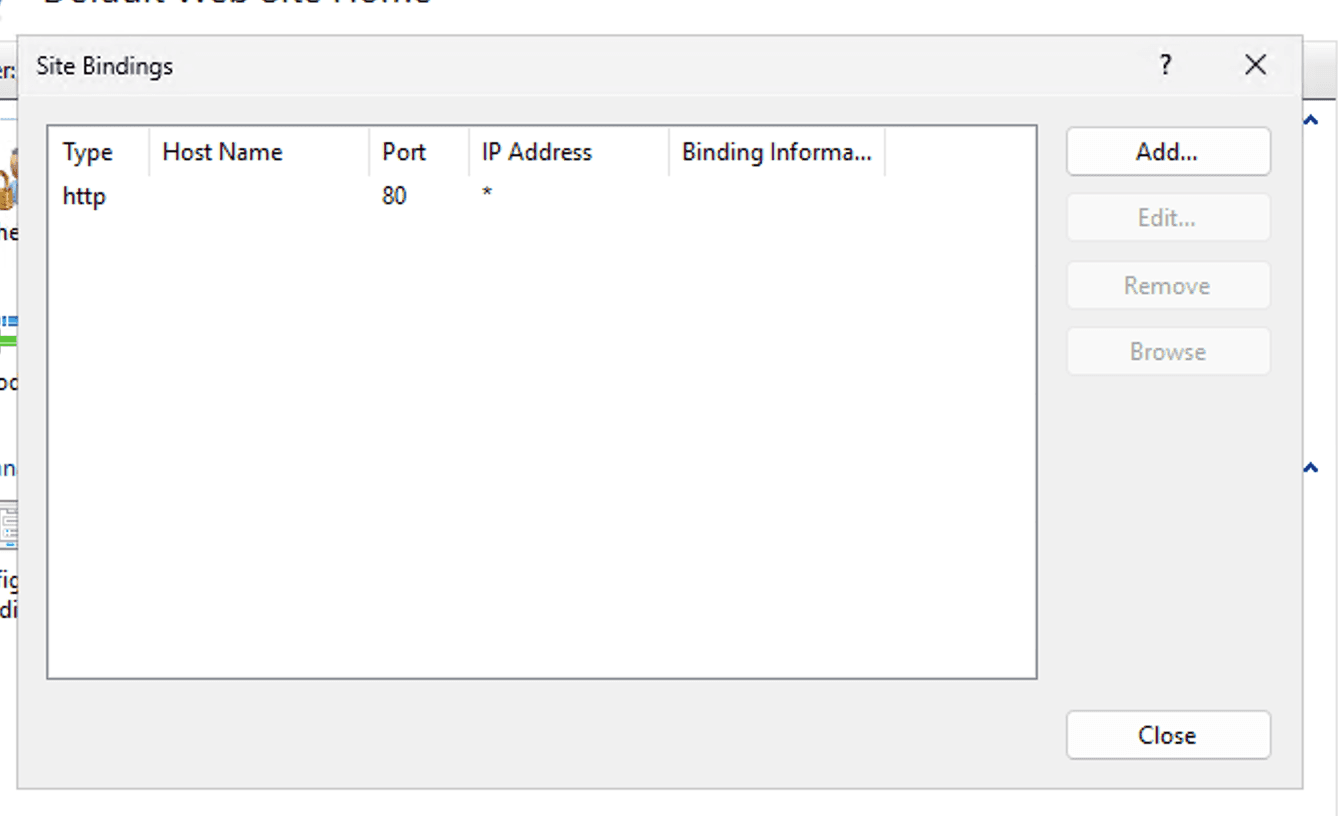
Finally, apply the certificate to the site running in test mode on IIS. Open the IIS Management Console, right-click the target site, and click Edit Bindings to open the settings screen.
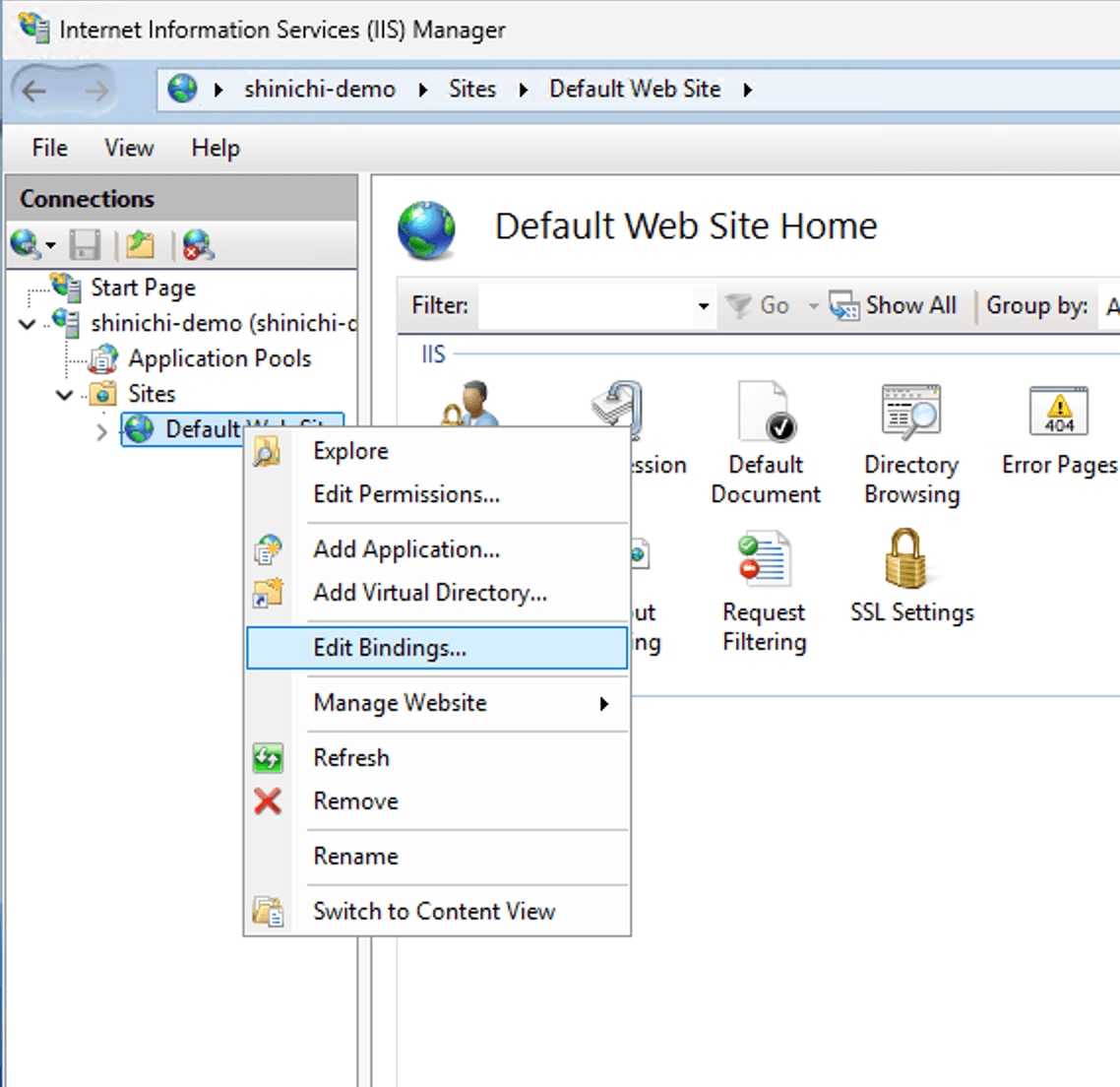
On the following screen, click the Add... button.
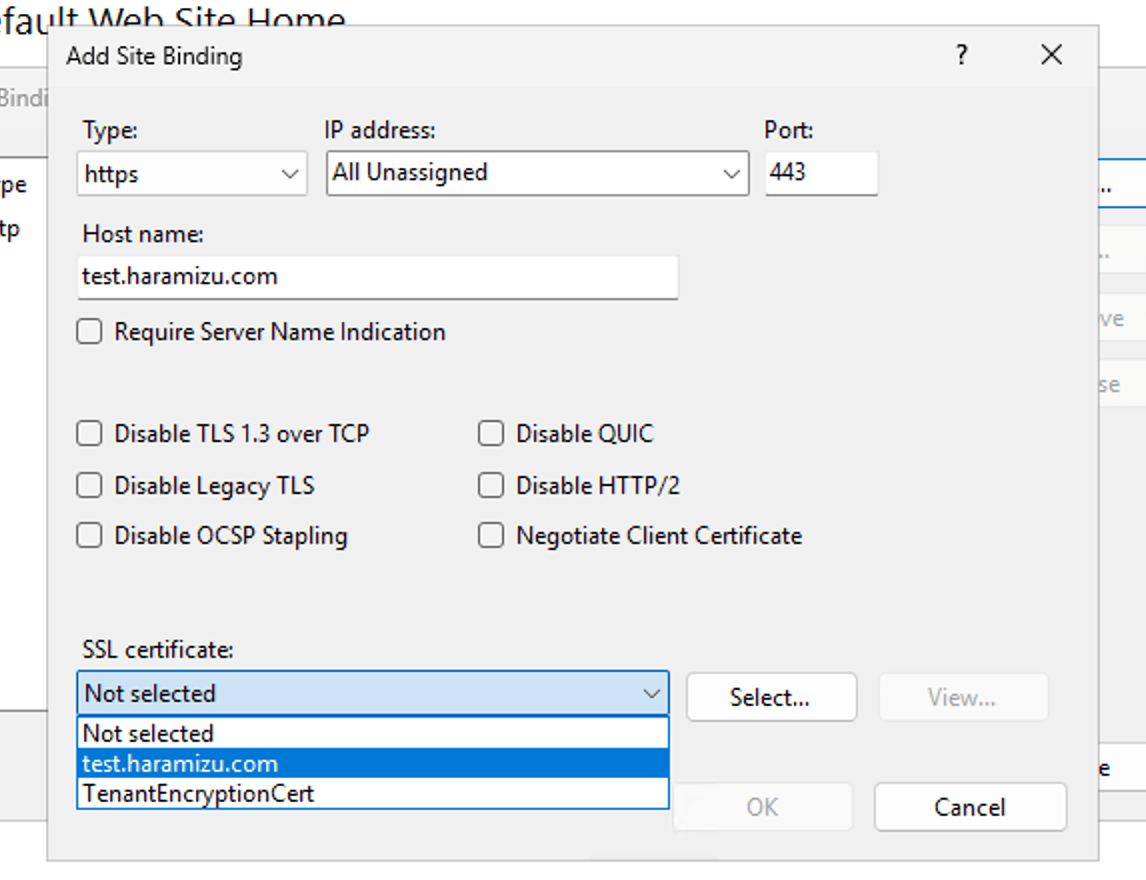
On the next screen, configure the settings as follows.
- Type: https
- For the Host name, enter the domain for which this certificate is being configured as its fully qualified domain name (FQDN).
- Select the installed certificate in the SSL certificate.
It is now accessible.
Functionality Verification
The certificate installation has been successfully completed. Verifying functionality was very straightforward; this time, I accessed https:// using the Chrome browser to check the certificate.
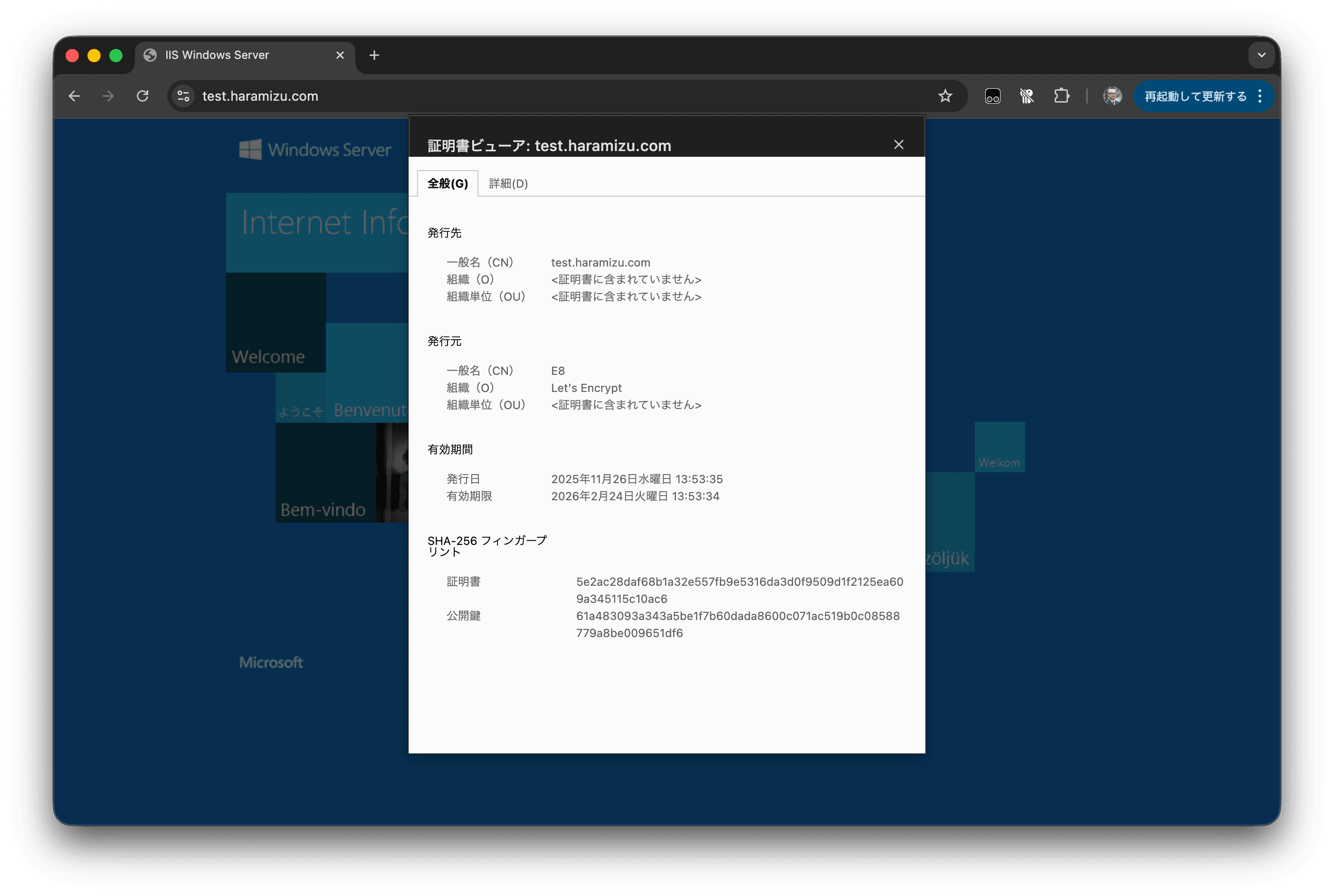
We have confirmed that it is operating with a Let's Encrypt certificate.
Summary
This time, we introduced the steps for creating Let's Encrypt certificate files on macOS. We also verified functionality by confirming that the site could be accessed using the certificate on IIS running in a Windows Server 2025 virtual machine.
The procedure itself is very simple, but the certificate period is short at 90 days. In a production environment, you will need to implement an automatic renewal mechanism or integrate with a service that automates certificate renewal. For limited-time operations like functional verification, this procedure should suffice.